Protecting Corporate Networks from Cyberattacks on Remote Access Services
A Large Number of Remote Workers Is a New Normality
The significant limitations of recent months have changed the usual workflows for many companies. Wherever possible, employees were transferred to remote work, giving them access to corporate resources, both from corporate and personal devices. Experience has shown that for many companies maintaining the ability to work remotely can be appropriate even after the removal of restrictive measures. International studies, such as the Global Workplace Survey, show an increase in productivity and a decrease in CapEx and OpEx.
All the achievements of companies in the field of ensuring remote work of employees during the period of restrictions in most cases will be in demand after the cancellation of those restrictions. All previously implemented technological solutions and the risks associated with them will also remain, so no one should expect the risks to disappear by themselves.
5 Ways to Steal an Account
The transfer of the business to remote work was immediately used by cybercriminals—significant outbreaks of attacks on VPN servers, computers of remote employees, and home Wi-Fi routers were recorded, the volumes of phishing and spam with malicious attachments also increased significantly. Why? The answer is obvious—it is easier for criminals to attack the least protected resources that appeared in connection with the time pressure associated with the transfer of employees beyond the usual corporate perimeter.
As a result of attacks on employees' devices, attackers can gain access to insufficiently protected credentials (login/password):
-
By guessing an account password using a bruteforce attack or by applying the password to other resources—in 60% of cases passwords are "duplicated"
-
By infecting an employee’s device with malware: a backdoor, keylogger, or Trojan
-
By hacking an employee’s home Wi-Fi router or by placing a dummy Wi-Fi access point in a public place
-
By watching/recording on video the employee’s connection to the corporate network in a public place
-
By using devices of employees of contractors and partners as the security requirements of their companies may be insufficient
A cybercriminal who has valid credentials gets the opportunity to "officially enter" the corporate network on behalf of the employee, which means they get full access to all internal resources of the company. It is much more difficult to identify such an attack since this requires the use of behavioral analysis and anomaly detection technologies requiring significant financial and time investment.
At the same time, the risks of compromising the credentials of employees and, consequently, the penetration of cybercriminals into the corporate network increase in direct proportion to the number of employees working remotely.
Weak link
During the RSA Security Conference’2020, Microsoft experts said that 99.9% of compromised accounts did not use multifactor authentication, although this is the most effective tool against bruteforce attacks. Their statistics are based on an analysis of more than 30 billion system login events per day for more than 1 billion users per month. According to the same analysis, in January of this year, 40% of hacks were associated with accounts with insufficiently complex passwords, and the other 40% were due to the reuse of passwords for various resources.
The conclusion is that one-factor authentication based on login/password is the weakest technological link in security systems, so you need to start by switching to strong multifactor authentication (MFA) based on one-time passwords (OTP), which adds an additional factor to the user authentication process that can neither be guessed nor replaced.
The ideal solution would be to go back in time to think through everything, calculate, and implement everything you need. But we don’t have a time machine yet, so we are looking for the most effective solution to provide the highest security level with the least time, resources, and costs.
3 Days to Deploy
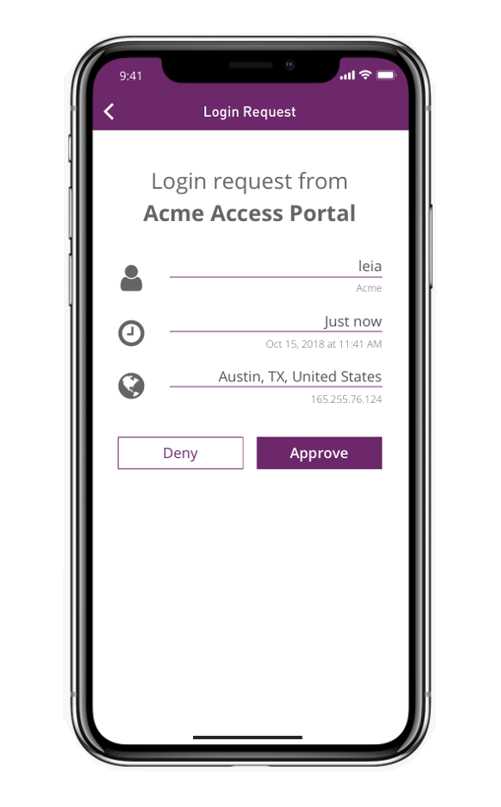
What are the implications of migrating to MFA in terms of time and resources? The main fears are most often associated with hardware tokens that must be purchased and delivered first to the company and then to employees who stay at home (in addition, accounting and administration are necessary, of course). But there is an alternative solution since you can use software tokens installed on smartphones from the usual Google Marketplace and Apple App Store. You can also send OTPs via text message or apply strong authentication without tokens. Any of these options speeds up deployment and reduces the cost of procurement and maintenance due to the lack of logistics of hardware tokens; at the same time, you can minimize the risks of losing or transferring the token to another person, especially in the case of using biometrics.
The best options for the client side have been determined, and now let's look at a management solution. There are two fundamentally different ways: cloud (the solution can be deployed in your private cloud) and corporate. But both of them imply integration with your RADIUS server that provides authentication for external connections through a standardized protocol. If you trust external cloud authentication services, the labor costs are minimal, you only need to connect and configure, and registering tens of thousands of users takes less than an hour. But if you prefer to control everything yourself, you need a mid-ranking server that can even be virtual because the average load is small. Its deployment and connection with our help won't take much time.
The best solutions: Try&Buy
There are many solutions, both foreign and domestic. In general, the criteria do not change: functionality/features, reliability, usability, and cost. The comparison will be quite large, and the analysis will take a lot of time. But we have already done this, so we will give only the most interesting offers.
 Thales is a world leader in this field. Last year, it merged with its closest competitor, Gemalto, which had previously taken over SafeNet. You can deploy the SafeNet Authentication Service solution on-premise or in a private cloud or use the authentication service from this vendor. The client side is SafeNet MobilePASS + Out of Band Push Authentication software tokens, text notification, or GrIDsure authentication based on a graphic template (we do not offer hardware tokens). Estimated price is less than $50 per user per year, including technical support. You will also receive a discount depending on the number of licenses and their validity. The solution can be tested free of charge for 25 days for 10 users.
Thales is a world leader in this field. Last year, it merged with its closest competitor, Gemalto, which had previously taken over SafeNet. You can deploy the SafeNet Authentication Service solution on-premise or in a private cloud or use the authentication service from this vendor. The client side is SafeNet MobilePASS + Out of Band Push Authentication software tokens, text notification, or GrIDsure authentication based on a graphic template (we do not offer hardware tokens). Estimated price is less than $50 per user per year, including technical support. You will also receive a discount depending on the number of licenses and their validity. The solution can be tested free of charge for 25 days for 10 users.

Indeed, one of the domestic leaders in this field, offers Indeed Access Manager with Indeed AirKey software tokens. It uses both foreign standards and cryptographic algorithms in accordance with GOST and can also provide a qualified electronic signature for authentication in the CryptoPro DSS cloud service. Estimated price of a license is about RUB 4,350 per user per year, depending on the available functionality and the number of licenses. The solution can be tested free of charge for 3 months for 30 users.
There are solutions from other well-known foreign vendors such as Fortinet FortiToken Mobile and RSA SecureID Software Token, but they are more expensive; while domestic solutions such as Aladdin and Rutoken require a hardware token, and CryptoPro offers the same AirKey.
There are MFA solutions that provide APIs for integration and other functionality. We will not list all of them because the list of our partners is huge, as is our experience in deploying such solutions. Most importantly, we have helped many private and state-owned Russian banks, consulting and investment companies, research centers as well as energy and mining corporations significantly reduce the risks of compromising information systems through the introduction of multifactor authentication.
Andrey Zerenkov, Information Security Expert, STEP LOGIC